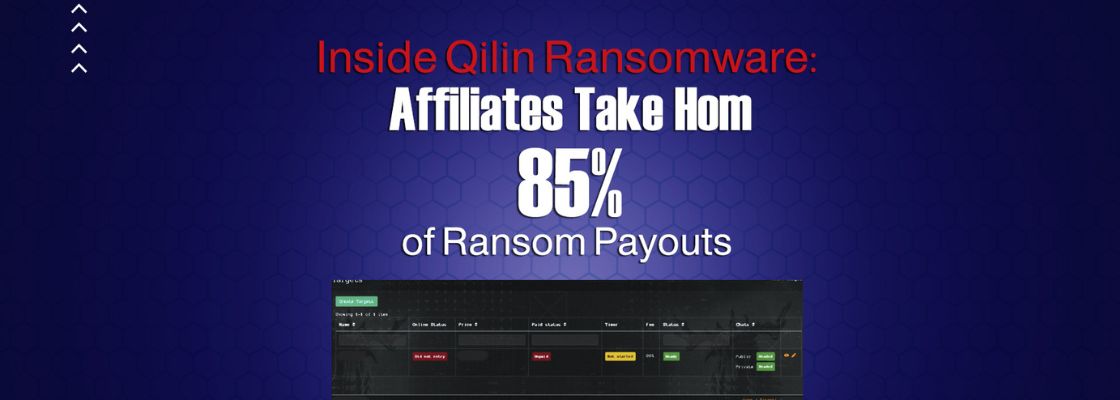
New findings from Group-IB shed light on the payment structure within the Qilin ransomware-as-a-service (RaaS) scheme, revealing that ransomware affiliates receive a significant share of each ransom payment, ranging from 80% to 85%.
Group-IB managed to infiltrate the group in March 2023, leading to insights into the payment structure and inner workings of the RaaS program, thanks to a private conversation with a Qilin recruiter known online as Haise. The cybersecurity firm’s comprehensive report states that Qilin ransomware attacks are often tailored to each victim, maximizing their impact.
The threat actors utilize tactics such as changing the filename extensions of encrypted files and terminating specific processes and services to achieve this customization. Initially documented by Trend Micro in August 2022, Qilin, also known as Agenda, started as Go-based ransomware before transitioning to Rust in December 2022.
The adoption of Rust provides the threat actors with enhanced evasion detection capabilities and allows them to target Windows, Linux, and VMware ESXi servers. Phishing emails containing malicious links serve as the entry point for attacks, enabling initial access and subsequent encryption of sensitive data. The group follows a double extortion model, exfiltrating the data before encrypting it.
Qilin’s data leak portal on the dark web has exposed data from at least 12 different companies between July 2022 and May 2023. The victims span critical infrastructure, education, and healthcare sectors, located in various countries such as Australia, Brazil, Canada, Colombia, France, Japan, Netherlands, Serbia, the UK, and the US.
Qilin actors provide affiliates, recruited to identify targets and carry out attacks, with an administrative panel to manage different aspects of their operations effectively. The affiliate panel includes sections for configuring ransom notes, managing blog posts, creating accounts for team members, posting news updates, tracking payments, and accessing support and documentation.
While Qilin ransomware has gained notoriety for targeting critical sector companies, it poses a threat to organizations across all industries. The ransomware operator’s affiliate program not only expands its network but also equips affiliates with upgraded tools, techniques, and service delivery capabilities, according to security researcher Nikolay Kichatov.